The Use of Self-Sovereign Identity With Zero-Knowledge Proof (ZKP)
A Use Case For Identity Verification
Our personal information is now mostly stored on computers, a result of the Digital and Information Age. Databases store millions of records that are hosted on servers in data centers which often belong to a private company or government agency. A person’s full name, DOB (Date of Birth) and SS (Social Security) data is often used to avail of services like credit, financing and medical treatment. Other personal information are very sensitive like when it comes to medical records. This information is often stored in silos on various servers shared by many offices. It is readily available for prying eyes to see, without regard to who it is. As long as the information is accessible, anyone can access it. Sometimes people who are responsible for safe guarding these digital records get careless for whatever reason and that neglect can lead to data breaches.
All this personal information has been entrusted to organizations and companies that should also be responsible for securing them. However, that is not always so, as in the case of Equifax. Data breaches are becoming so common, it is assumed that millions of records have been exposed. This leaves people vulnerable to identity theft, credit fraud and cyber-crimes. Hackers who can obtain this information can use it to make illegal purchases on a person’s credit cards.

With the many checks and balances in place today to curb hacking attempts, it is not always perfect. A system can be compromised in many ways and they often involve lax security and poor cybersecurity practice. Data is the gold that hackers want to steal because information is both empowering and valuable as a resource in today’s world. There has to be a better way to protect it.
What can we do about this? Does anyone other than the government, that provide us service, need to really see our sensitive information?
Individuals are often not in control over their own identities. Personal information is regularly shared without the person knowing about it. Banks, merchants, creditors and agencies regularly share our information for review purposes like in the case of applications for loans and mortgages. There are instances though when this information is shared for ad targeting and marketing purposes, without us knowing about. Employers also have the personal information of their employees sitting on servers used by the HR department.
Sometimes data is shared and sold without the individual’s consent. Even Facebook unethically sold user information to third party buyers, who then gathered insights from them for more devious purposes e.g. Cambridge Analytica 2016 US elections. The information is already stored in a database, which is mostly centralized. This also makes it a target for hackers despite security measures that have been put in place to meet compliance and regulations. That doesn’t mean it is totally secure and safe. To further secure it, blockchain technology is one way to prevent tampering with information.
We don’t need to have it transparent for the world to see, but we could use a verification system to make that information available to others without them knowing what that information actually is. This is called “Zero-Knowledge Proof” or ZKP. We provide our information only to the government and then it is cryptographically secured on a blockchain using a hash function. That way only the hash value will be available to those who want to verify your identity without having to see your personal information.

This can be implemented as a system called Self-Sovereign Identity with Zero-Knowledge Proof. This allows individuals to have complete control of their personal information without having to reveal it to others. Although government requires it to prove citizenship and personal identity, they do not have to be shared with every company or agency that requests it. What is happening is that personal information is being sent to other places where they are stored on servers that may not be secured. It then only takes one exploit by hackers to get that information, so it can be risky despite efforts to secure them. What Self-Sovereign Identity with ZKP proposes is to obscure the actual information while verifying the individuals identity.
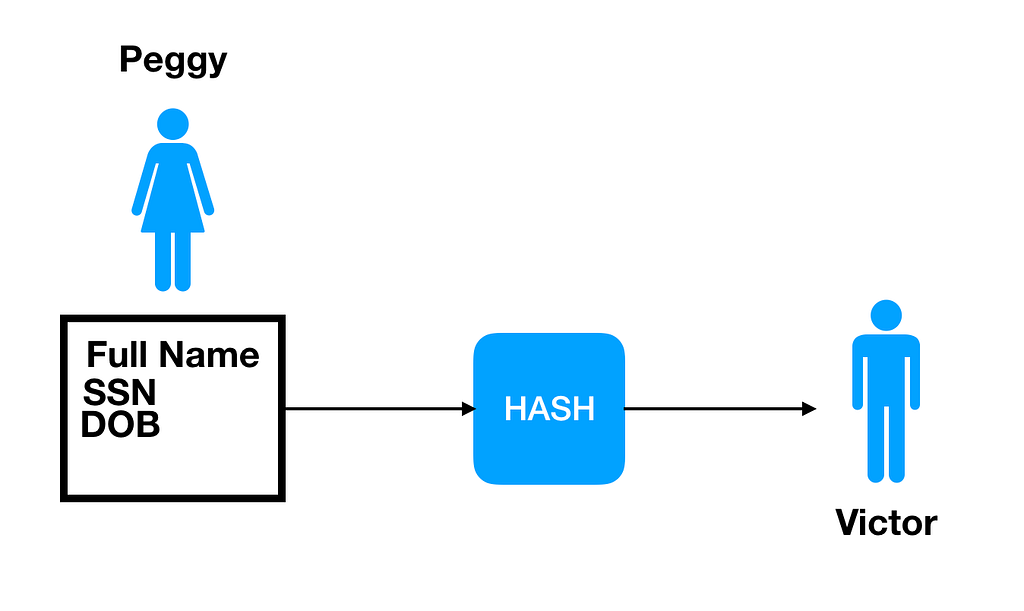
With Zero-Knowledge Proof, we have a prover, who is the individual, and a verifier, who needs to verify an individual’s identity. In this case, all the prover needs to show a verifier is the value of X, without showing the actual information. All this requires is a proof of knowledge to verify that the individual is who they claim to be. This is a form of digital fingerprint that can prove an individual’s identity. The validity of the proof lies in using a cryptographic hash function that proves without a doubt that the identity is valid.
When you use a hash function on a set of variable data, as in the case of personal information (they are not all the same length), the output can be consistently of a fixed value. Therein lies the verification, because tampering with it is highly improbable, requiring extreme computing power or luck. When data is hashed, the inputs cannot be easily determined based on the output. In the case of Self-Sovereign Identity, the individuals personal information can be stored in a private database that can even be centralized under the government. However, the information is then hashed and the value is stored on separate database that is public and uses a blockchain.
The reason a blockchain is used in this scenario is to provide a transparent, immutable, reliable and auditable way to share the public information. This can implement a ZKP protocol that allows provers (individuals) to feed a hashed value to verifiers (credit companies, banks, hospitals, etc.) in order to provide identification. In the process the verifiers will know it is correct without having to actually see it. The way this works is the public database will store the hashed value on a distributed decentralized network of nodes, that have validated the information through a consensus mechanism. This is required to establish the truth. Verifiers will then compare the hashed value from the prover to the hashed value stored on the public blockchain. So one might argue that it is easy to know an individuals personal information, even their social security number.
To further secure the information requires the use of a digital private key that only that individual can possess. This is then required to “unlock” the information to prove to the verifier their identity. The private key is also hashed along with the personal information, and the output value should always be unique. Individuals will be identified by their “public address” which is calculated from a unique private key that no one else has.
With a system that verifies identity without revealing the actual information, there are plenty of advantages for online transactions. Individuals will have to worry less about their digital identity being stolen when they transact business on the Internet. When individuals manage their own information, it decentralizes who controls it and where it is stored. Less control and less points of failure when individuals are allowed to take control of their own digital identity. Another advantage of using an identity system is that it can interoperate with other systems to verify an individual’s identity. It would be much faster and requires less hassle and data entry on computer systems. With digital identification systems, the verification process can be over with in seconds.
Think about how fast it would be to apply for a new credit card without having to fill out so many forms and entering redundant information that is already stored in a database. This sort of system provides a more accurate and efficient way of verifying identity that is also more secure. It can also limit or prevent data breaches since the verifier does not need to see an individual’s complete personal information. On the verifier’s side, their developers can create an API to access personal information with authorization to auto-fill forms, etc. That is just one of many possibilities that can provide solutions to digital identification systems.

Individual’s do have a “right to privacy” or the “right to be left alone” as stated in amendments made in 14th Amendment of the US Constitution:
“No state shall make or enforce any law which shall abridge the privileges or immunities of citizens of the United States; nor shall any state deprive any person of life, liberty, or property, without due process of law; nor deny to any person within its jurisdiction the equal protection of the laws.”
Individuals have a right to their own personal information that is free from public scrutiny, without a third party involved that could see or control the information.
One other implementation of self-sovereign identity with ZKP is in digital identity verification for compliance with KYC and AML rules. Many financial institutions, including banks, have this requirement to meet SEC and other governing regulations. Its all about proving identity, but at no risk when using ZKP. All the information required is verified and that is all that needs to be known.
The examples given are a more simplified explanation of Self-Sovereign Identity with Zero-Knowledge Proof without delving into the details. The system I described is not even fully decentralized since there is government control of an individual’s personal information due to the issuance of social security numbers, etc. In the future though, it can all be decentralized and automated by computers without requiring the government to know anything other than the hashed output value. In this scenario, as soon as an individual is born, they are assigned their own digital identity. There are many theories on this that I cannot cover here, so there are many possibilities to explore in order to fully secure personal information.
Suggested Reading:
The Equifax Data Breach
https://www.ftc.gov/equifax-data-breach
Blockchains and Self-Sovereign Identity
https://www.computerworld.com/article/3244128/security/how-blockchain-makes-self-sovereign-identities-possible.html
Zero-Knowledge Proof Explained
https://www.tokens24.com/cryptopedia/basics/the-zero-knowledge-proof-explained
https://medium.com/media/0707f5c806284d01a4a13c7b13a91ce3/href
Self-Sovereign Identity With Zero Knowledge Proof was originally published in Data Driven Investor on Medium, where people are continuing the conversation by highlighting and responding to this story.