How the FBI evades transparency and accountability when handling victims’ funds
“Bless your heart” is a phrase that is common in the Southern United States. The phrase has multiple meanings. It can be used as a sincere expression of sympathy or genuine concern. It can also be used as a precursor to an insult to soften the blow. It is also sometimes used to mean “you are dumb or otherwise impaired, but you can’t help it” by individuals who wish to “be sweet” and do not wish to “act ugly.” ―Wikipedia
This video pretty much sums it up:
https://medium.com/media/145e9f270b0c7dc1fe015d2679356aca/href
The FBI has previously mishandled bitcoin

In March 2015, two agents were indicted for stealing digital currency during their investigation of the Silk Road, an underground black market on the dark web that facilitated a variety of illegal transactions. Former U.S. Drug Enforcement Administration agent Carl Force was tasked with an investigation of the Silk Road. Force later pleaded guilty to charges of extortion, money laundering, and obstruction of justice for stealing bitcoins during the probe and for secretly soliciting payment from Ross Ulbricht, who ran the black market.
Carl Force used fake online personas and engaged in complex Bitcoin transactions to steal from both the government and the targets of the investigation. Specifically, Force allegedly solicited and received digital currency as part of the investigation, but failed to report his receipt of the funds, and instead transferred the currency to his personal account.
He ultimately tricked Ulbricht into paying him more than 1200 bitcoins, which would be worth more than 70 million USD today. That pales in comparison to the whopping 3100 bitcoins (182 million USD) stolen by Shaun Bridges while he investigated Ulbricht’s connection to the site. Both of these men believed that the cryptocurrency was “untraceable” and could not be linked back to their identities. Indeed, they would have gotten away with it if they had just taken one extra precaution. Their downfall was their failure to use a tool called a Bitcoin mixer.
Find out how this one weird trick gets crooks off the hook

A Bitcoin mixer, more accurately called a cryptocurrency tumbler, is a service that mixes potentially identifiable or “tainted” cryptocurrency funds with others, so as to obscure the trail back to the original source of the tainted funds. Cryptocurrencies like bitcoin provide a public ledger of all transactions, so these tumblers have arisen to improve their anonymity. The existence of tumblers has made the anonymous use of dark web markets, such as the Silk Road, easier, and the job of law enforcement harder.
Agents Force and Bridges were only identified and caught once they had sent their coins to an exchange for the purpose of converting their stolen property to cash. Indeed, as Ars Technica has reported, “when Force opened Bitstamp account #557042 on October 12, 2013, it sealed his fate.” Exchanges are typically required to follow AML/KYC regulations and do not permit customers to open an account without first providing some identifying information.
When law enforcement agents are able to identify coins involved in illicit transactions on the blockchain, they can simply trace them to an exchange and serve the exchange with a subpoena in order to identify the criminals. However, a Bitcoin mixer makes it far more difficult to connect the funds that were involved in illicit activities with the funds that eventually make it to the exchange.
Mixers effectively obscure the traceability of prior bitcoin transactions as an intermediate step taken before sending them to an exchange. If those federal agents had taken this step, they could have effectively put enough distance between themselves and the tainted transactions to evade detection. Authorities would have been unable to serve the exchange with a subpoena for the transactions, because after mixing their tainted coins would have been diluted with untainted coins.
Mixing makes the job of identifying the criminal entities who are tied to tainted funds on the blockchain all the more difficult.
The FBI learns from its past mistakes

When the federal authorities seize funds in a forfeiture, you would think that transparency would be a high priority, for the sake of the victims. You would be wrong. The FBI now routinely uses Bitcoin mixers both before and after a seizure, which completely contradicts the opinion of the DOJ. This procedure means that the victims must blindly trust the FBI as they have no way of verifying exactly how much funds the FBI actually seized from the criminals. It also makes it very difficult for other law enforcement agencies to audit the FBI when they take possession of illicit funds. The rest of this article will examine a specific case where the FBI’s use of a Bitcoin mixer provides no known benefit, either for the victims who are eligible for remission or for law enforcement itself.
When law-abiding citizens use Bitcoin mixers to preserve their privacy, they are accused of violating anti-money laundering laws. If FinCEN is criminalizing Bitcoin mixers because it believes that law-abiding citizens should not use them, then why is the FBI using them? The evidence that the FBI is using them is clear. What is unclear is the FBI’s motives. What we do know is the policy which permits them to “mingle” or “mix” together cryptocurrency funds from multiple sources into one aggregate fund. The following is taken from the 2019 Asset Forfeiture Policy Manual:
The commingling of cash seized by the Government under 21 U.S.C. § 881(a)(6) will not deprive the court of jurisdiction over the res. Unlike other assets seized by the Government (e.g., real property, conveyances), cash is a fungible item. Its character is not changed merely by depositing it with other cash. While it is true that the jurisdiction of the court is derived entirely from its control over the defendant res, court jurisdiction does not depend upon control over specific cash.
It has never been a requirement that the Government segregate specific cash seized for forfeiture in one case from that seized for forfeiture in another. Commingling of such assets has been the rule and not the exception.
The specific case in question
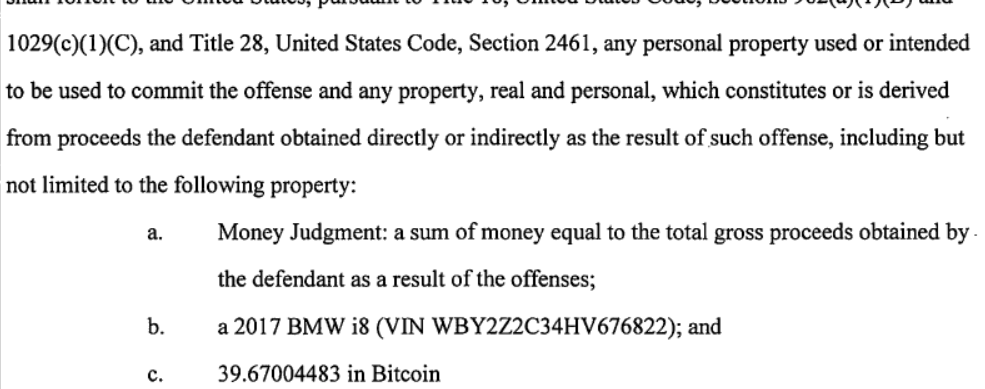
On August 01, 2018, the FBI seized 39.67004483 Bitcoin from Ahmad Wagaafe Hared in Tucson, AZ for forfeiture pursuant to 18 U.S.C. 981(a)(1)[C]. The same forfeiture amount of 39.67004483 Bitcoin later appears in an indictment against Mr. Hared and Mr. Matthew Gene Ditman. They were later convicted of committing unauthorized SIM swaps to steal and extort cryptocurrency from victims. They operated as part of a group that specialized in tricking or bribing representatives at the major wireless providers into giving them control over phone numbers belonging to people who these thieves later targeted for extortion and theft.
The Money Laundering and Asset Recovery Section (MLARS) of the DOJ manages the FBI’s Asset Forfeiture Program. This includes distributing forfeited funds and adjudicating petitions for the remission of forfeited assets. The FBI sends out updates to victims, and recently the victims of Hared and Ditman were asked by the FBI to submit their petitions for remission in light of their convictions.

Unfortunately, the way the FBI listed these funds in their database made it seem as if the cryptocurrency had been already sold. When the seizure notice was sent out in 2018 the FBI claimed it had 39.67004483 Bitcoin, but recently, when the victims filled out their form online, the FBI claimed to have a “Financial Instrument — Virtual Currency” valued at $255,731.58 which is exactly 85% of the value listed at the time of seizure. The FBI takes its cut of 15% before it gives the victims anything, which is why some of the victims felt that the “clerical error” in the FBI’s systems implied that the asset had been sold shortly after it was seized. The 34 bitcoin the victims believe they are entitled to would be worth 2 million at the time of writing. 255 thousand vs. 2 million is one hell of a clerical error (UPDATE: these funds have NOT been converted, please see note below).
The FBI implied that the value of the cryptocurrency as shown in its database was incorrect, but how could the victims know for certain if the FBI even still had possession of these funds? They had to check it on the blockchain. That’s when they found a transaction for, you guessed it: 39.67004483 Bitcoin on January 3rd, 2018. Wait, that can’t be right. The FBI claimed it had seized these funds in August of 2018, yet the blockchain shows that the funds were seized in January. Yet another clerical error? The FBI published this erroneous date in its official notification posted on October 23, 2018, as well as in a letter sent to the victims.
The transaction in question
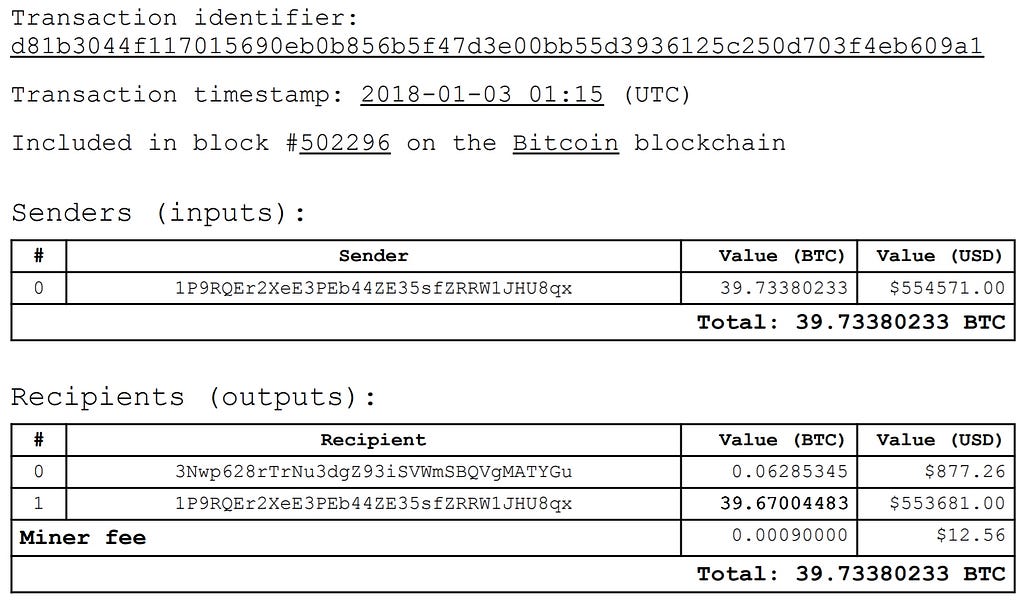
This transaction occurred on January 3rd, 2018 and there are a few things that seem odd about it:
- The sender 1P9RQ…U8qx is sending funds to themselves
- It’s coming from an address that has sent more than 800,000 transactions
- It’s coming from an address that has sent more than 43 million bitcoin
To put things in perspective, there are only 21 million bitcoins that will ever exist. Processing 43 million bitcoin would require this address to receive the equivalent of the sum total of all bitcoin that will ever be mined through this address twice. Put another way, they could have moved 10% of all the bitcoins which have been in circulation the past 5 years through this address 30 times. In other words, they could send 1% of all bitcoins that have ever been mined in human history through this address 231 times. Now that’s a lot of tumbling!
1P9RQEr2XeE3PEb44ZE35sfZRRW1JHU8qx put in perspective
According to this research paper, the most popular bitcoin address is 1dice8EMZmqKvrGE4Qc9bUFf9PX3xaYDp (SatoshiDICE 48%). It has processed a total of:
- 3,195,823 transactions
- 1,020,333 BTC in value
and it saw a peak balance of 2.5K bitcoin in early 2013.

According to another research paper, the most popular bitcoin address is 1VayNert3x1KzbpzMGt2qdqrAThiRovi8 (deepbit.net). It has processed a total of:
- 786,936 transactions
- 25,467,612 BTC in value
and it saw a peak balance of 3.3K bitcoin in early 2012.
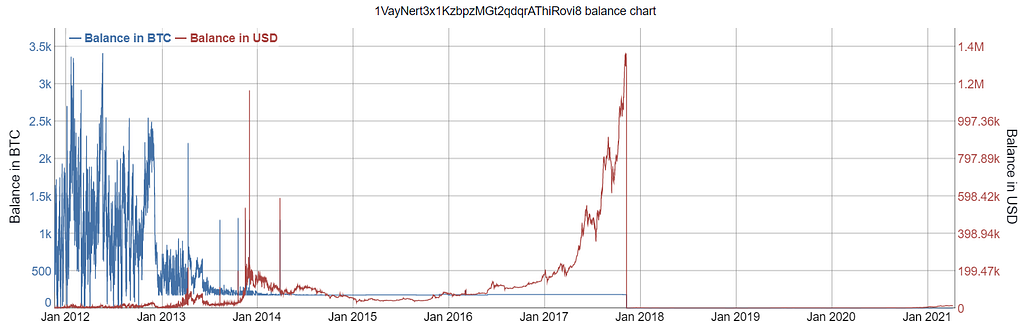
Why is it that no one has ever noticed the volume of transactions on the FBI’s Bitcoin address? It has processed a total of:
- 825,872 Transactions
- 43,163,411 BTC in value
and it saw a peak balance of 16K bitcoin in the Summer of 2017.

Why I don’t want the FBI sending my money through mixers
Whenever someone I don’t personally know tells me to “just trust them” I get a bad feeling. I don’t know you, I’ve never met you, we haven’t spent any meaningful time together. Recently the FBI has been under public scrutiny, how many Americans can say that they fully trust the FBI today? I’d like to point out that what the FBI is doing may not be legal. Some people believe it may violate the Financial Integrity Act of 1982, which states:
(d)(1)(A) To ensure compliance with the requirements of subsection (a)(3) of this section, internal accounting and administrative controls of each executive agency shall be established in accordance with standards prescribed by the Comptroller General, and shall provide reasonable assurances that —
(i) obligations and costs are in compliance with applicable law;
(ii) funds, property, and other assets are safeguarded against waste, loss, unauthorized use, or misappropriation; and
(iii) revenues and expenditures applicable to agency operations are properly recorded and accounted for to permit the preparation of accounts and reliable financial and statistical reports and to maintain accountability over the assets.
To be 100% clear, the FBI does not need a money transmitter license to act as a lawful Bitcoin tumbler. Government agencies are exempt from needing to obtain a Money Services Business (MSB) license. However, what I’d like to humbly point out is that the law requires funds to be “safeguarded against waste, loss, unauthorized use, or misappropriation.”
The question of what constitutes “waste” is a crucial one. The FBI has custody of victims’ funds, but it would not be appropriate to pay fees in excess of a certain threshold to obfuscate transactions. I have no idea of what this threshold might be, but obfuscating transactions through a tumbler typically incurs additional transaction fees paid to miners. These fees are 2 to 5 times higher than they would be if the transaction was not obfuscated. Why should the victims be required to pay excess fees to Bitcoin miners? These fees are deducted from the total available funds which were seized at the time of forfeiture, so the victims cannot get them back. It is very expensive to tumble Bitcoin and the victims never asked the FBI to use their funds in this way.
How expensive is it? Well, the FBI chose to tumble these funds at literally the most expensive time in the past 5 years (or ever?). I’m no expert on this topic, but if you compare the chart below with the chart from bitinfocharts for the FBI’s address there is some mighty suspicious correlation going on between these two!
The chart below compares January 2018 and August 2018. You might remember that the FBI told the victims that they confiscated these funds on August 1st, 2018, but the blockchain says that these funds first appeared on January 3rd, 2018. If we assume that these funds were tumbled a few days prior to January 3rd, then the FBI overpaid bitcoin miners by a factor of 4700%! This is relative to what they would have paid if they waited to tumble them on August 1st. Now multiply that by 2x to 5x, the additional fees to obfuscate these transactions. That’s a lot of fees!

In summary
I don’t have anything against the FBI. I don’t hate the FBI. I just hate the feeling of being treated like a child who needs to stop complaining and trust the authorities. Yes, we do need to trust authority figures, but those authority figures should first work to earn our trust. Those authority figures should also try their best to be accountable, and as transparent as possible. If the FBI would just use the blockchain the same way they expect the rest of us to use the blockchain, we would get the following benefits:
- Victims would be able to identify the transaction that moved the funds from the criminal’s address to the FBI’s address. This would allow them to know exactly what funds were actually seized.
- Victims and other interested parties would be able to verify that 100% of the funds which were promised to the victims were paid to the victims.
- Other government agencies would be able to easily audit the FBI and could provide reports facilitated by the blockchain that would serve to ensure transparency and accountability.
I’d be more than willing to trust the FBI if they’d simply take the time to answer my questions over the phone. To be honest, I’ve been pestering the agents on my case, perhaps a bit too much, and they were really nice to me even though I was a total jerk. The individuals in the FBI more decent human beings than I am. But this policy about cryptocurrency tumbling must be reevaluated and brought into the public light!
There is a lot more I’d like to say, but I need some time to process all of this. As it pertains to this matter, more than anything I wish that I had a better relationship with the FBI. I just want them to listen to me and have an honest conversation. I don’t care about the money. I care about the fact that crucial pieces of evidence that could have expedited their investigation were ignored or dismissed as unimportant. I did my best to understand how T-mobile’s policies enabled the thieves to steal these funds, but everyone treated what I had to say as nonsense. This made me feel stupid and frustrated.
In closing, I’m making this request of anyone reading this:
Let’s work together to hold our government agencies accountable. They should commit to not using cryptocurrency tumblers unless they have a good reason to do so. If they do have a good reason, they should tell us what it is and not treat us like children.
UPDATE NOTE: The FBI has stated unequivocally in an email that the funds are still held as Bitcoin. They are required by law to hold these funds as Bitcoin and not convert these funds to cash. Please see the 2019 AFPM and see the following section:
Because of the risks that early conversion may pose, in most cases, cryptocurrency should be kept in the form it was seized and not … converted to fiat currency … until a final order of forfeiture is entered or an administrative forfeiture is final. Agencies or prosecutors may, however, seek an order for the interlocutory sale of virtual currency at the request and/or consent of all parties with an ownership interest in the cryptocurrency.
Special thanks go to:
Baheej Anwar — research
Dan-Andrei Stangaciu — research
Lila Sadkin — editing help
Dear FBI, God bless your heart was originally published in DataDrivenInvestor on Medium, where people are continuing the conversation by highlighting and responding to this story.